What is RSA/DSA SSH key?
SSH is a cryptographic network protocol for initiating text-based shell sessions for secure data communication and/or remote command execution. This connection is useful when user isn’t physically present near the machine. As far as I know, any network service can be secured with SSH. The SSH key consist of public and private key pair. The public key is placed on computer that must allow access to the owner of the matching private key. Therefore private key must be kept private at all times. When you first time setup secure connection to any device, it will send you its public key, so you can also decrypt messages from them.
How it works?
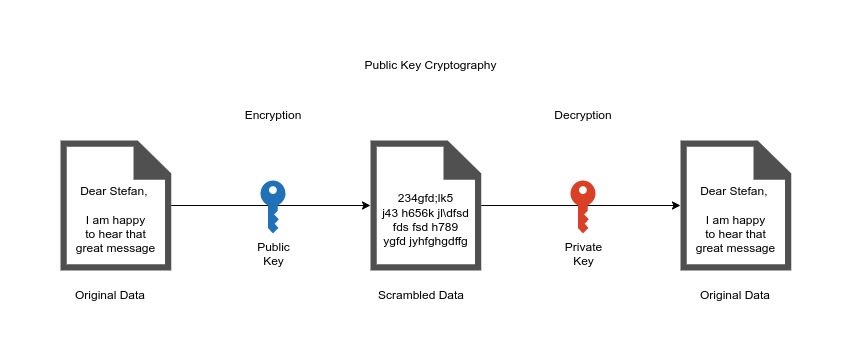
When any message is sent out, it is firstly signed with your private key. So the message leaves your computer in HASH-ed version which is encrypted and the content of message is unreadable. The message travels through internet in this HASH-ed form and noone can read it. When the message is finally received by recipient, they can’t read it until they present the matching public key and only that key can decrypt hashed message and make it readable. This means that the message left your computer encrypted and was readable only by someone who owns your public key. When the other side sends message to you, they will sign it with their private key and send the HASH-ed version to you. When you receive it, you have to use their public key to decrypt it. This happens all around, until the secured communication isn’t closed. Person in the middle, somewhere on internet, who would like to track your communication can’t see anything reasonable from reading your messages. As you can see, the messages are not sent to central authority, but are sent directly between the two connected parties. This type of connection is called peer-to-peer connection. This public-key cryptography is also known as asymmetric cryptography.
How can I generate RSA/DSA SSH key?
On linux you can use tool ssh-keygen which is usually part of the linux installation.
Step 1 - Create the RSA or DSA key pair
Just type in terminal:
ssh-keygen
or if you want to generate DSA key use:
ssh-keygen -t dsa
The -t option specifies the type of key to create. Use the above to create DSA key. If you want to generate RSA certificate you don’t need to use this option as RSA is default type. For more options you can simply run
ssh-keygen --help
Step 2 - Select filename and passphrase
Enter file in which to save the key (/home/stefan/.ssh/id_rsa):
First you will be asked to select filename. The default key name is id_rsa and because we are happy with this filename, we just press Enter.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
You will be asked to enter your passphrase and then confirm it. Even if the keygen allows you to create SSH key without passphrase, I would advise you to enter password. The only protection of private key is that it is not visible to anyone else, because the permissions of file are set this way (I will show you later). The benefit of passphrase of SSH key is, that if your private key somehow falls into unauthorized users possession, they will be unable to use it, until they figure out the passphrase. This gives you extra time to generate and install new key pair, before the hacker will do. The only downside to having a passphrase is that you will need to enter it each time you use this key pair.
Your identification has been saved in /home/stefan/.ssh/id_rsa.
Your public key has been saved in /home/stefan/.ssh/id_rsa.pub.
The key fingerprint is:
6b:7f:3e:93:f7:4a:4d:b7:c7:78:7b:9d:8d:60:fb:26 stefan@freya
The key's randomart image is:
+--[ RSA 2048]----+
| .oo. |
| . o.E |
| + . o |
| o . |
| S . + + |
| . . . o E.|
| o. ..+= B|
| o . +..o =o|
| .. ..+o o. |
+-----------------+
Step 3 - Find your new SSH key pair
When you check now your .ssh folder in home directory you should have there two new files there
stefan@freya:/var$ ls -la ~/.ssh
total 20
drwx------ 2 stefan stefan 4096 Jul 1 19:34 .
drwxr-xr-x 24 stefan stefan 4096 Jul 1 18:06 ..
-rw------- 1 stefan stefan 1766 Jul 1 19:33 id_rsa
-rw-r--r-- 1 stefan stefan 394 Jul 1 19:33 id_rsa.pub
-rw-r--r-- 1 stefan stefan 664 Jul 1 19:41 known_hosts
The id_rsa file is the private key file. As you can see, it has -rw------- permissions, which means that only owner can read and write this file.
The other file id_rsa.pub is your new public key file.
We learned in part 1 how to create SSH keys, in the next Part 2, we will learn how to install them on servers and how to use them Disclaimer: You shouldn’t share these keys with anyone else.